What are the differences between Internet Gateway and NAT Gateway?
Introduction
Networking in AWS is complicated. Understanding AWS networking concepts and how they work together is essential to ensure that your services are secure and have internet connectivity.
Before looking at the differences between Internet & NAT Gateway, let’s go through AWS networking fundamentals.
Table of contents
- Introduction
- AWS Virtual Private Cloud (VPC)
- What is Network Address Translation?
- Internet Gateway (Igw)
- NAT Instance
- NAT Gateway
- Conclusion
AWS Virtual Private Cloud (VPC)
A VPC is your private network within AWS. A VPC isolates your resources from everyone else’s.
Each AWS account comes with a default VPC that is pre-configured for you to start using immediately. A VPC can span multiple availability zones in a region.
A VPC only exists in one AWS region.
CIDR Blocks
When creating a VPC, you must specify a range of IPv4 addresses for the VPC in the form of a Classless Inter-Domain Routing (CIDR) block. E.g., 172.31.0.0/16 is the primary CIDR block for your VPC. It defines 65536 IPv4 addresses in your VPC.
Subnets
A subnet is a range of IP addresses in your VPC. The subnet must use a CIDR block that falls within the assigned VPC.
You can create multiple subnets within a VPC. A subnet can logically group resources based on your requirements.
There are two types of subnets:
Public Subnet: Resources in a public subnet can be accessed from the Public Internet.
Private Subnet: Resources in a private subnet cannot communicate with the public internet.
Route Table
Route Tables contain the rules (routes) determining how network traffic will be directed within your VPC and subnet.
Each subnet is linked to one Route Table.
What is Network Address Translation?
Network Address Translation (NAT) allows you to map multiple local private addresses to a unique public IP address. This single device acts as an intermediary between the local, private network and the public internet.
Internet Gateway (Igw)
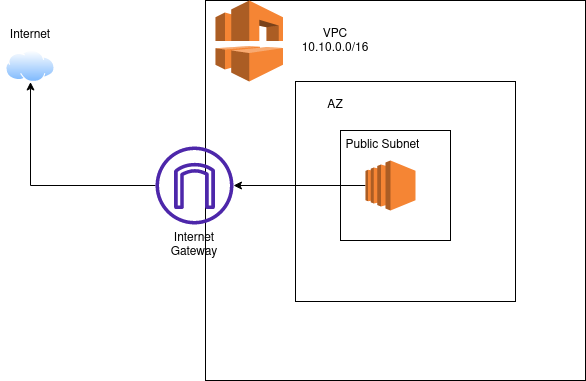
Internet Gateway is a VPC component that allows communication between your VPC and the Internet.
An Internet Gateway is a logical connection between an AWS VPC and the Internet. There is no underlying physical resource.
Each VPC has only one Internet Gateway. If a VPC doesn’t have an Internet Gateway, then resources cannot be accessed from the Internet.
A Public Subnet is a subnet that is associated with a route table that redirects traffic to an Internet Gateway. Therefore, its important to ensure that your route tables are configured correctly.
Why is an IGW important?
- Enables Inbount and Outbound access to the Internet
- Performs Network Address Translation (NAT) for public instances
- Horizontally Scaled, Redundant & Highly available
Pricing
Internet Gateway is simply a logical router to the internet for a VPC. You pay for all outbound internet traffic, but there is no fee directly associated with the IGW.
NAT Instance
A NAT Instance is a self-managed Amazon EC2 instance that is configured to act as the intermediary between your private subnet and the public internet.
The NAT instance has to be in the public subnet. Instances in a private subnet that want to access the Internet will forward their internet-bound traffic to the NAT instance using the Route Table configuration.
Since such an instance is self-managed, you would be responsible for configuring routing and updating the software amongst other similar tasks.
NAT Gateway
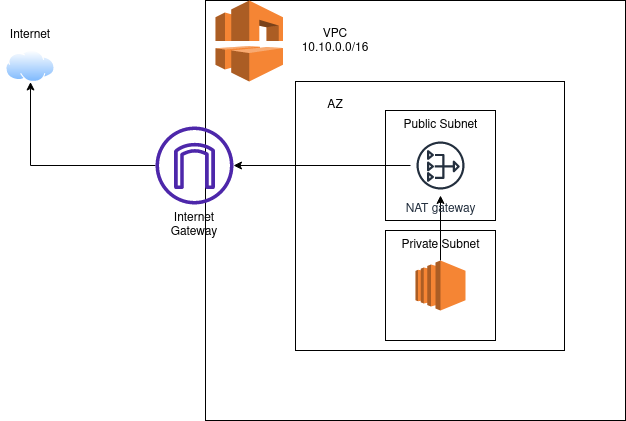
NAT (or Network Address Translation) Gateway is a managed AWS service that is used so that instances in a private subnet can connect to services outside the VPC. These private resources don’t allow any inbound traffic from the public Internet.
NAT Gateway was introduced, so users no longer have to manage their own NAT instance. The benefits of using a NAT Gateway service are:
- Fully-managed service: You no longer need to manage your own NAT instance
- Supports 5 Gbps bandwidth and automatically scales up to 100 Gbps.
- You cannot associate a security group with a NAT gateway.
NAT Gateway allows two connectivity types:
- Public: Instances in private subnets can connect to the internet through a public NAT
- Private: Instances in private subnets can connect to other VPCs through a private NAT gateway. More details can be found here .(https://docs.aws.amazon.com/whitepapers/latest/building-scalable-secure-multi-vpc-network-infrastructure/private-nat-gateway.html)
This article will focus on the Public NAT Gateway to keep things simple.
A Public NAT gateway is created in a Public Subnet. An Elastic IP address is associated with the NAT Gateway when it is created.
If you have multiple Availability Zones (AZs) in your AWS Architecture, you must create a separate NAT Gateway in each AZ.
A NAT Gateway relies on your Route Tables to be able to route traffic to the public Internet. It is important to create a route from the NAT Gateway to the Internet Gateway to ensure proper Internet connectivity.
How does request routing work with a NAT Gateway?
- Private Instance in a private subnet initiates the connection to the Internet.
- The request to the internet goes through the NAT Gateway in the public subnet.
- The NAT Gateway uses its public IP address to access the internet. It acts as the source of the request.
- The NAT Gateway routes the request to the public internet via the Internet Gateway.
- The response goes to the NAT Gateway.
- The NAT Gateway forwards the response to the private instance that made the request.
Pricing
Unlike the Internet Gateway (IgW), a NAT gateway incurs charges based on the creation and the usage of a NAT gateway in the user’s account. More details about NAT Gateway pricing can be found here.
Conclusion
To summarize, the key differences between an Internet Gateway and NAT Gateway are:
- IgW allows both inbound and outbound access to the internet whereas the NAT Gateway only allows outbound access. Thus, IgW allows instances with public IPs to access the internet whereas NAT Gateway allows instances with private IPs to access internet.
- You only need one Internet Gateway per VPC whereas you need one NAT Gateway per Availability Zone (AZ)
- There is no additional cost to use Internet Gateway whereas NAT Gateway incurs charges based on the creation and usage.